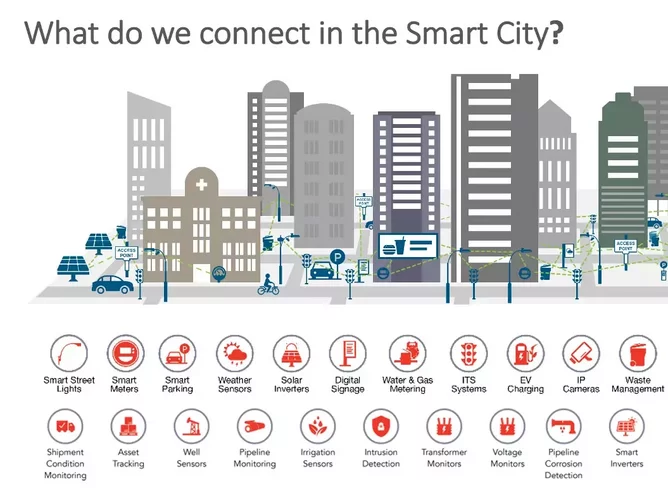
Is it possible to build secure smart cities?

IoT technologies are finding their way into every part of our lives, from factory production lines, to smart home applications and smart city design. Security-by-design and open standards should be the guiding principles when building IoT systems. These will not only help to minimise cyber risk, but can also speed time-to-market and drive cost efficiencies.
We are in a new era of creating and building smart cities. Yet as connectivity and computing power is distributed more widely across large-scale outdoor networks, threat actors will scale-up their own operations. A Nokia report last year shows that internet-connected, or IoT, devices now make up around a third of infected devices, up from 16% the previous year. The report’s findings are based on data aggregated from monitoring network traffic on more than 150 million devices globally.
Weak passwords, vulnerabilities and insecure networks continue to blight deployments, providing attackers with an opportunity to sabotage critical infrastructure, hold organisations to ransom and steal sensitive data from connected networks. Perhaps the first example of this was in the 1969 film, The Italian Job. Traffic on the streets of Turin is brought to a standstill as a criminal gang sabotage the ‘smart city’s’ traffic signalling and camera surveillance network.
Unfortunately, real life is worse and we are already seeing the impact of cyber attacks. Earlier this year, we saw an attack on a water plant in Oldsmar, Florida designed to poison residents’ drinking water. More recently, a hack was able to take down the largest fuel pipeline in the US, leading to shortages across the East Coast.
In this context, engineers and developers must focus on developing a robust security architecture based on two key elements: device authentication and encryption.
Each device must be uniquely identifiable so that it can be authenticated effectively when joining a network, and able to prove that it has not been tampered with or hijacked with rogue code. Digital certificates embedded in each device are the best way to achieve the former. Passwords should be avoided at all costs as they can be easily stolen or cracked.
All secure devices must contain a private key, but this is also an Achilles heel from a cyber risk perspective. How can you mitigate against this? Consider a Hardware Secure Element — a chip designed specifically to protect against unauthorised access, even if the attacker has physical access to the device, as is often the case with IoT.
Another technique to prevent tampering is the Physical Unclonable Function (PUF). Here, a ‘fingerprint’ is derived from the unique characteristics of a piece of silicon. This can then be turned into a unique cryptographic key and used as the chip’s root key. The advantage here is that no additional hardware is needed to store the key securely, and that it becomes invisible to hackers when the device is powered off.
But don’t forget encryption. At Wi-SUN Alliance, we build AES encryption into radio chips to scramble messages on the fly, reducing power consumption and processor overhead, while maximising data security.
It’s also worth considering network topography at the design stage. Mesh networks offer several advantages over star (or hub and spoke) networks. More reliable because data can be re-routed a different way if devices lose contact with each other. Transmissions are typically made over shorter distances so there is improved power efficiency and performance. With Wi-SUN we have frequency hopping functionality that makes it difficult for an attacker to deny service by jamming signals.
The final piece is to focus efforts on open, interoperable standards. From a security perspective, this means specs will be mature and reliable, stress-tested and verified by many users, and vulnerabilities are quickly detected and remediated.
From a hardware perspective, following open standards can speed time-to-market, keep costs down and also ensure products are usable with a variety of manufacturers’ processors and radios. There will be a whole host of existing publicly available protocol stacks, design information and reference implementations to help build and future-proof secure products.
As smart cities and smart utilities continue to evolve and large-scale corporate IoT networks continue to grow, so will the attention of those looking to bring them down or hold the to ransom. Security-by-design must be non-negotiable when designing and building them.